Innovation in the Crosshairs: The First Six Hours of AI and Cyber Governance in Malaysia
TLDR;
AI governance requires clear guardrails. Enterprises are focusing on defining data ownership, access controls, and security boundaries around AI systems rather than leaving governance as an afterthought.
Cybersecurity teams play a critical role in enabling AI safely. While model development sits with data and business teams, security teams focus on preventing data exposure, enforcing policy guardrails, and ensuring systems remain protected.
Large enterprises often operate across multiple compliance frameworks. Organizations must align global policies, industry standards, and local regulations, driving a need for integrated governance approaches and centralized oversight.
Incident readiness is increasingly important. Leaders emphasized the need for clear playbooks, defined reporting responsibilities, and tested response procedures to ensure organizations can respond quickly during cyber incidents.
It was 4 PM in Putrajaya when a quiet alert pinged the operations dashboard. Within minutes, teams would need to decide: a system glitch, or the first sign of a cyberattack?
Last Thursday, AIBP, together with SoftScheck, convened enterprise leaders in Putrajaya, and that sense of urgency set the tone for the discussion. Cybersecurity, AI adoption, multi-framework compliance, and incident readiness are now boardroom priorities.
And the stakes are real.Companies operating across critical national infrastructure face fines of up to RM500,000 for major violations, with non-compliance potentially carrying prison terms of up to ten years. Yet, competitive pressure is relentless. According to the AIBP Cybersecurity Report, 76% of Malaysian enterprises see moderate to significant AI investment as essential even as concerns over data privacy, security, and ethical AI use weigh heavily on decision-makers.
AI Governance: Start with the Fundamentals
As enterprises experiment with AI, leaders emphasized the importance of building defining boundaries and governance on solid foundations rather than reacting after risks emerge. Organizations must be clear on who owns the data, who can access it, and what safeguards are in place.
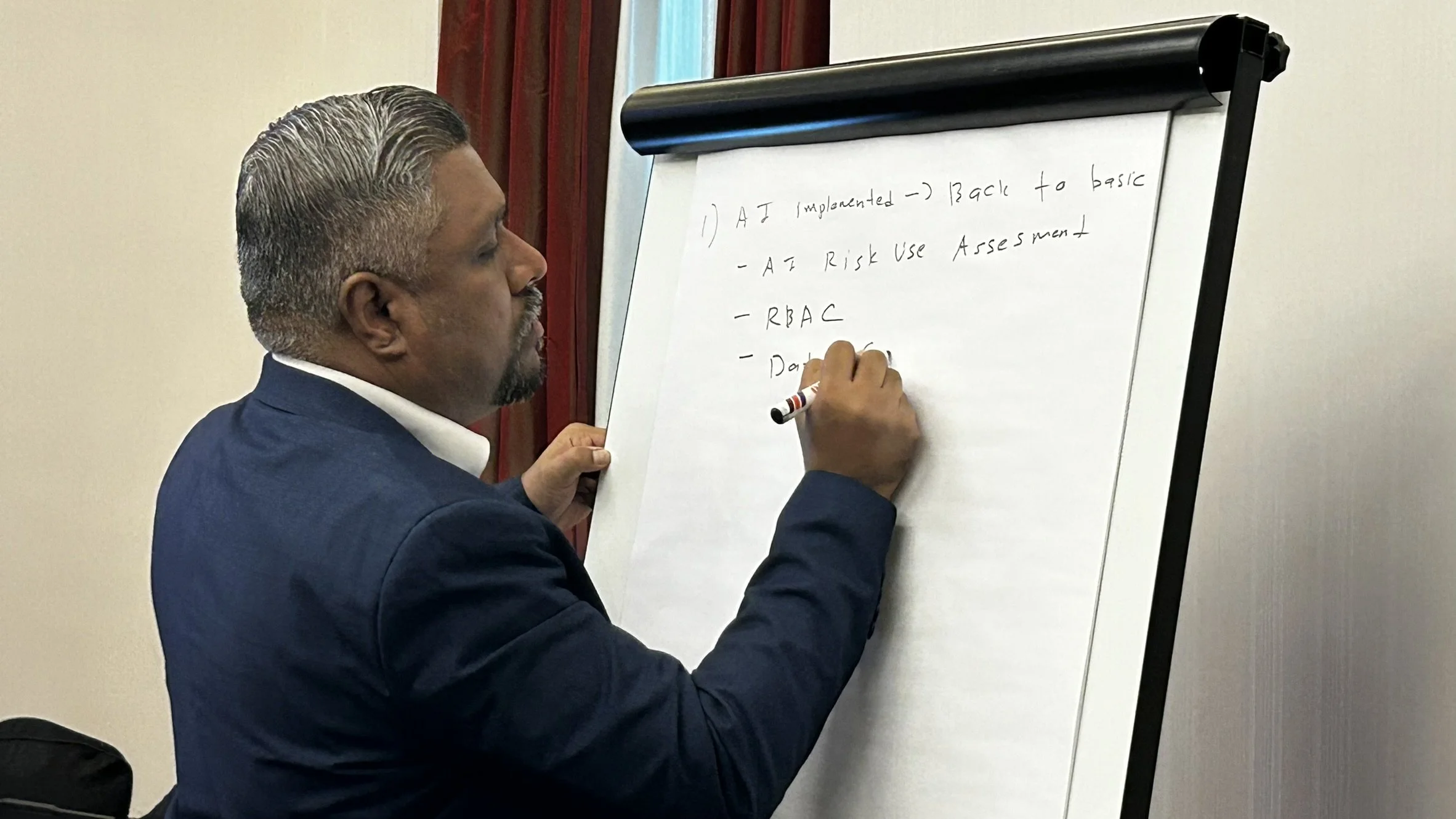
Dr. Nishan Surentharan, Senior Manager of Business System & IT Governance from IOI Group notes that the best step is return to the basics.
“Identify who the data owners and users are, and work backwards from there. Implement role-based access controls and review your existing AI governance framework. Most organisations have already done data classification, so always refer back to that.”, shared Dr Nishan.
In practice, IOI has implemented regular AI risk assessments. They send evaluation forms to users periodically and require system integration risk assessments for partners or vendors before deploying any AI solution. These steps form the controls and guardrails that guide safe AI adoption.
This reflects a broader enterprise approach where AI adoption must be accompanied by structured governance, vendor assessments, and data oversight.
Azril Rahim, Cybersecurity Director from Tenaga Nasional Berhad (TNB) offers a complementary perspective, emphasising proactive governance and operational oversight.
“Governance is always on the prevention side. In our service meetings, we review every AI project’s guardrails to ensure data protection and operational safety before deployment.”
They also coordinate with data owners and trainers, ensuring that the AI systems are properly integrated while minimizing cyber and operational risks. This pre-emptive approach allows TNB to balance innovation with security, rather than waiting for incidents to occur.
Multi-Framework Compliance: Integrate, Don’t Overload
For organizations operating across sectors and geographies, compliance fatigue is real. Companies must juggle global parent policies, local regulations, and industry standards simultaneously. Without centralized oversight, teams can become overwhelmed, duplicated efforts pile up, and critical risks slip through the cracks.
Jason Leong, Cybersecurity Manager from AEON Retail Malaysia shared how they navigate this complexity: Besides Japan group policies, we also have local audits and regulatory requirements. We follow ISO and PCI standards. There are many frameworks we need to comply with at the same time.
Jason highlighted that the challenge is not cultural resistance but standardization across multiple frameworks. To manage this, they are evaluating integrated systems that consolidate audits and compliance requirements, reducing operational stress on teams while ensuring alignment with Japan’s J-SOX reporting obligations.
Their approach emphasizes practical tools and centralized oversight, not just policies, ensuring teams can focus on actionable compliance rather than administrative burden.
Hans Raj, Programme Director from CIMB reinforced the importance of a continuous, centralized view: Audit is not a one-day thing. It’s an ongoing process. If you are always prepared, you don’t have to scramble when auditors arrive.
CIMB maintains a cross-country perspective, tracking compliance readiness across Malaysia, Singapore, Indonesia, and the Philippines. This allows them to see how teams are performing, identify where support is needed, and prevent operational overload. Rather than leaving local teams to navigate complex audits on their own, CIMB provides practical guidance and tools, ensuring that compliance is managed efficiently while freeing teams to focus on strategic initiatives, such as AI adoption.
Incident Readiness: What Happens at 11PM?
Cyber incidents are rarely convenient. The first six hours often dictate whether a minor event escalates into a crisis.
“When there is an incident, we report first,” Azril Rahim said. “Sometimes we don’t yet know if it’s a cyberattack or system failure. But it’s safer to report early and let authorities determine the classification.”
SoftScheck, as conveners of the discussion, added a broader perspective on incident readiness:
“In the first hours, the focus should be on identifying affected systems, confirming the scope, and initiating containment, documentation comes next. It’s about acting quickly and strategically, not perfectly.”
They emphasised that for less mature organizations, having a structured approach and predefined roles can make the difference between a reactive scramble and a confident, coordinated response.
Innovation and compliance are not opposing forces. Enterprises that invest in foundational governance, consolidate compliance frameworks, and prepare to respond immediately to incidents are able to pursue AI and digital transformation with confidence.
In the end, it is the discipline, foresight, and operational maturity of those who manage both. In a world of accelerating digital risk, the ability to act with speed, clarity, and integrity may be the ultimate competitive advantage.
If discussions like these spark your interest, catch up on our 2025 Conference & Exhibition highlights on Data Governance and Cyber Resilience:
Day 1: Responsible AI, Strategic Readiness, and Cyber Resilience in Focus
Day 2: Sustainable, Secure, and Skilled: Building Malaysia’s Digital Advantage
Register your early interest for the July conference here.
Fill in the form to connect with us